Your customers trust you to deliver the products and services they need for their business. Often, this means they give you their personal information so you can receive payments, provide solutions, or help them in other ways.

Whether your organization processes payment cards, provides healthcare, or offers any other services, protecting customer information should be your top priority. Depending on your service and industry, you'll collect different types of data for various uses — and each kind of data comes with its own nuance for protection.
The first step to protecting customer data is understanding the types of data customers share with you. From there, you can learn about the guidelines and laws in place to help you provide customers with security and get the most out of their information as you help your organization continue to thrive.
Overview of protected information
Personally identifiable information (PII), personal health information (PHI), and payment card industry (PCI) data are different categories of information that organizations can use to identify individuals and provide them with a service. PII, PHI, and PCI all fall under the category of information governance. Governance is defined as the security regulations organizations must follow to protect sensitive client information and stay transparent about its use.
Your business or organization likely collects and accesses customer information daily. Whether customers are using their credit cards to purchase your products, patients are receiving treatment at your medical facilities, or people are sharing their personal information with you for marketing reasons, they're trusting you to keep their data as safe as possible.
In exchange, you receive the benefits of their data — their interests, their demographics, and other non-identifying information you might use for research and marketing. Collecting customer data also helps your organization run more efficiently and recognize your costs. Information governance helps you capitalize on the inherent value of personal information by minimizing risks and optimizing customer data to reach your goals.
PII, PHI, and PCI each have their own set of compliance standards that allow organizations to get the most out of their customer data while keeping it secure from cyber threats. These standards encompass security measures and industry practices while helping organizations stay within legal bounds to control information sharing and help avoid accompanying risks.
The financial sector and PCI
The payment card industry Data Security Standard (PCI DSS) is a security standard that payment card brands worldwide use to process, store, and transmit cardholder data securely. PCI DSS is included in the security protocols of all credit cards to protect cardholders from card fraud and identity theft.
Why PCI DSS?

Credit and debit cards are some of the most common ways to make payments. When customers pay you for a product or service, they expect to be protected. However, vulnerabilities can exist anywhere in the card-processing process, including:
- Point-of-sale devices
- Personal devices like computers and cell phones
- Internet connections
- Online shopping websites or applications
- Paper storage
- Data transmission to a third-party service you've partnered with
PCI DSS protects cardholder data through technical and operational requirements that apply to all people and businesses involved in payment card transactions. The standards ensure all involved entities protect the cardholder, including merchants, payment processors, card issuers, card service providers, and any other entities that receive, process, store, or share cardholder information.
As a PCI DSS-compliant company, you can protect your clients' cardholder data by preventing data breaches, which can also help you improve your brand reputation to gain more clients.
How does PCI DSS secure information?
PCI DSS protects all payment card account data provided in-person or over the internet, including:
- The primary account number (PAN) typically found on the front of the card
- The card's security code
- The "Full Track Data" stored in the card's chip or magnetic stripe
- The cardholder's personal identification number (PIN)
- The cardholder's name
- The card's expiration date
Some of the major requirements for PCI DSS-compliant organizations include:
- Installing and maintaining firewalls
- Implementing secure password protection
- Protecting stored cardholder data
- Encrypting transmission of cardholder data between parties
- Regularly updating antivirus programs
- Maintaining secure systems and applications
- Restricting access to cardholder data to only secure, compliant businesses that need the information
- Providing unique IDs to those with access to the data
- Restricting physical access to cardholder data
- Monitoring who accesses network resources
- Regularly testing security systems
- Creating a written information security policy for all personnel
These requirements ensure protection during direct card-to-system transactions as well as the resulting flow of information to different parties across the internet.
To ensure as much protection as possible, credit card companies and their third-party entities must undergo yearly formal risk assessments to identify any potential threats to and vulnerabilities of cardholder information. Risk assessments let your organization stay up to date on cardholder data security so you can continue to protect your customers in an ever-changing world.
If your organization operates under PCI DSS, you must also manage any outside service providers you share cardholder information with. Third-party services must acknowledge their responsibility to protect cardholder data, and you must annually monitor their security standard compliance to make sure they're providing your customers with a safe card payment experience.
Healthcare compliance and PHI

Protected health information, or PHI, is health-related information created or received by any entity covered by health privacy statutes. PHI is any data, including demographic information, that relates to:
- A person's past, present, or future physical or mental health
- The healthcare a person receives
- The payment for a person's healthcare
- Related information that can be used to identify the person, such as their name, address, birth date, and Social Security number
Why PHI protection?
Health organizations are required to protect PHI, whether it's included in written documents or in spoken conversations between patients and healthcare providers, or between healthcare providers and other entities they work with. Since data about people's health allows you to provide individuals with the best care possible, keeping this information organized and secure is vital.
Healthcare-related information governance also ensures that if you need to transmit a patient's health information to third parties, such as billing companies, lawyers, and accountants, it will still be secure throughout transmission and only go to third parties that will uphold the same security standards.
The Health Insurance Portability and Accountability Act (HIPAA) is a common statute covering most people's "individually identifiable health information" stored or transmitted by many healthcare organizations. Within the healthcare system, entities that must follow HIPAA regulations to ensure patient data security include:
- Health plans
- Most healthcare providers that conduct businesses electronically
- Healthcare clearinghouses where the patient has to allow the release of any data included in the 18 HIPAA identifiers
How do PHI protections secure information?
If any of the following types of information, known as the 18 HIPAA identifiers, appear in a written document or spoken conversation related to an individual's healthcare, this information cannot be released to the public without patient permission:
- Patient names
- Geographic location information such as a street address, city, county, precincts, and ZIP codes
- Dates, excluding individual years, that directly relate to an individual, such as their birth date, admission date, discharge date, and death date
- Phone numbers
- Fax numbers
- Email addresses
- Social Security numbers
- Medical record numbers
- Health plan beneficiary numbers
- Account numbers
- License numbers
- Vehicle identification numbers
- Device identification numbers
- URLs
- IP addresses
- Biometric identifiers such as fingerprints
- Full-face photographs
- Any other unique identification numbers, codes, or characteristics that could be used to identify a person, such as passport numbers
HIPAA regulations are critical because they provide a baseline for data security that directly affects people's quality of care. HIPAA-protected PHI lets people receive the healthcare they need without interference from security breaches on an individual or organization-wide level.
PII compliance for every industry
PII is information that can directly identify an individual, such as someone's name, address, Social Security number, phone number, email address, or any other identifying number or code. PII is also information that an entity can use to identify individuals in conjunction with other pieces of data, such as gender, race, birth date, and geographic location. Any contact information for an individual that can be used to find them physically or online is also PII.
Information that isn't specific enough to be considered PII on its own can become PII when combined with other readily available information that, together, might successfully identify an individual.
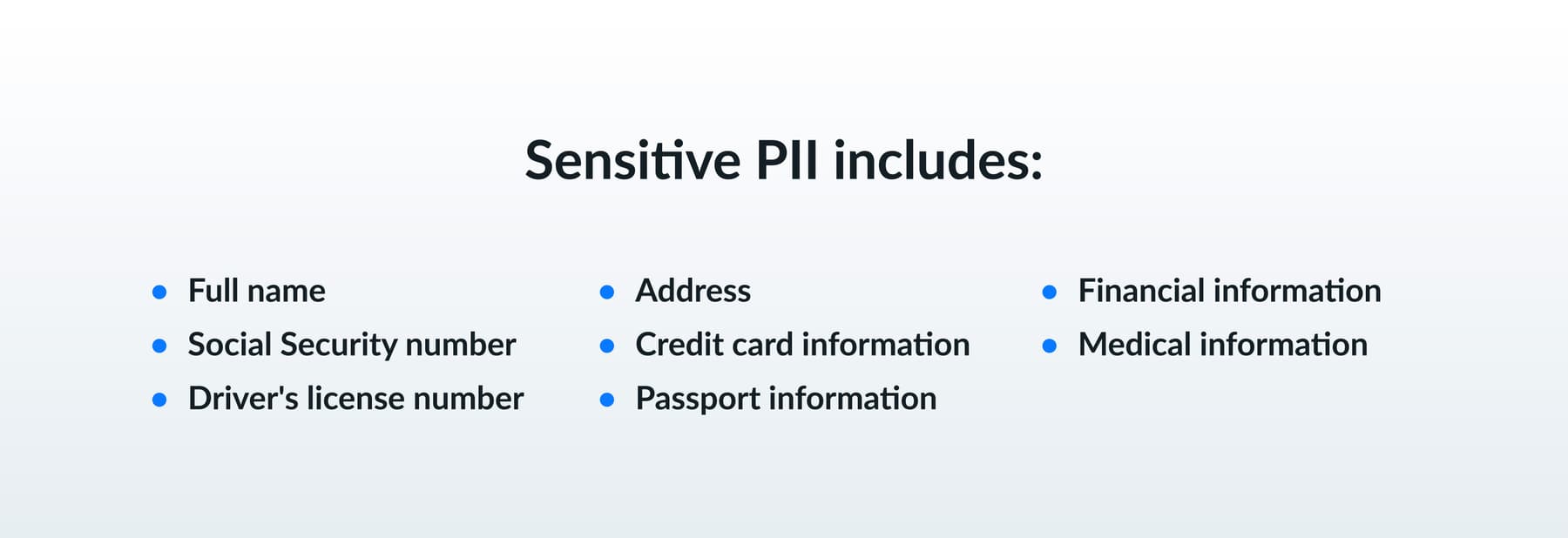
PII can be divided into two categories — sensitive and non-sensitive. Sensitive PII includes:
- Full name
- Social Security number
- Driver's license number
- Address
- Credit card information
- Passport information
- Financial information
- Medical information
Non-sensitive information includes:
- Race
- Gender
- ZIP code
- Date of birth
- Birthplace
- Religion
Non-sensitive PII can be released on its own without putting the individual at risk for identification. However, if not carefully monitored, non-sensitive PII can be linked with other data to reveal a person's identity. Your organization should always take care to safeguard PII of any kind and only release it if absolutely necessary.
If your organization collects customers' personal information, your area's laws may legally require you to uphold certain security standards to protect the PII from unauthorized access, use, destruction, changes, or other data breaches.
Many states also have regulations directing how you should discard customer PII. Your state may have specific instructions for PII disposal, or it may require you to have your own plan. Either way, taking steps to protect PII even after you no longer need it is important for retaining customer trust and freeing up data storage space.
The importance of protecting customer information
In today's interconnected world, personal information flows more freely than ever before, with service providers and cloud computing expanding the ways organizations like yours access and use customer data. The internet speeds up communication and makes all forms of PII, from social media information to e-commerce data, more shareable.
You have an increasing responsibility to protect your customers by understanding the different security protections and third-party relationships available to you. You can best protect your customer data by selecting third-party relationships that will contractually uphold your organization's security standards and monitoring those relationships to make sure they stay compliant.
People's personal information affects their daily lives. Finances, health information, identification numbers, and more are all components of personal data that people need to keep secure for their lives to run smoothly and for them to access necessary services like payment cards, healthcare, and Social Security benefits. When you protect your customers' data, you ensure your organization's services are trustworthy when they need it most.
Keeping updated with security standards and conducting customer relationships accordingly lets you provide a secure customer experience you can continue to improve as technology allows. When creating an information governance plan, your legal responsibilities also help you build a good business strategy and establish healthy customer relations.
Creating an information governance plan
To determine the security plan you need, look at the way you use customer information, why you need that information, the risks of collecting that information, and the benefits of having that information. From there, you can create a plan to best avoid foreseeable risks and be prepared with potential solutions to any issues that arise.
Many state and federal data security laws require organizations to implement data security safeguards, data breach notification systems, privacy notifications, and privacy consent forms. Data breach notifications let you inform your customers of any threats to their personal information. Keeping customers updated and fixing any issues establishes you as trustworthy.
Similarly, consent forms and opt-out options inform customers of any risks they'll face while doing business with you and give them options for how they'd like to receive your services based on the information they provide. Being honest and transparent with your customers increases their loyalty to you. Protecting customer information keeps customers safe and helps your organization stay reputable.
Comparing PII, PHI, and PCI
While PII, PHI, and PCI all require forms of information security, they each operate in slightly different ways. PII is the overarching type of customer personal information, with PCI and PHI as specialized subsets of PII security in the financial and health industries, respectively.
PII, PHI, and PCI are similar in that their standards all require your organization to perform a minimum amount of disclosures and uses of customer data. Customers give you their information trusting you will keep it secure and only share it with authorized parties when absolutely necessary.
PII vs. PCI

Since PCI is a category of PII, the PCI DSS is just as rigorous as the standards for other types of sensitive personal information. However, the PCI DSS also differs from PII security in several ways, as the PCI DSS are standards specific to the payment card industry.
When do they overlap?
The PCI DSS covers PII when the PII is related to cardholder data. Some personal information falls under both categories, such as cardholder names and card PINs, as well as any other identifying information on the payment card. As financial details are considered PII, those details also fall under the category of payment card information, and the PCI DSS protects them in financial contexts.
When do they not?
All payment card information is PII, but not all PII is protected by the PCI DSS. An individual's identifiers, such as their name and address, are often included on payment cards and the related paperwork and can certainly help identify individuals when combined with their financial information. However, non-financial identifiers on their own, outside of financial contexts, are not PCI.
Other types of personal information are protected in different ways. For instance, any medical-related documents and conversations are PHI and aren't protected by PCI DSS unless connected to information strictly related to payment cards, such as PINs.
PII vs. PHI

PHI is a category of PII directly related to health information. PHI protection standards are just as rigorous as those protecting PII and payment card information, but health information security standards are limited in the types of personal information they protect.
When do they overlap?
PHI security standards often cover PII, since documents like medical records and hospital bills include personal information to identify health data content with the correct people. Regular PII is necessary to include with medical documents to ensure people receive the care they need, are treated appropriately based on relevant personal information such as their age, and are billed correctly.
When do they not?
Similar to the distinction between PII and PCI, personally identifiable information alone isn't automatically categorized as PHI. A person's name, for example, can exist in non-health-related contexts. However, a person's medical records, which include their name, are always considered PHI.
The exception to PHI security protections is when the medical information of a large group of people is used anonymously in a collection of aggregate data, without individual identifying information. Medical institutions often compile data from real people to use in studies. In these cases, researchers ensure any information released to the public cannot be directly traced back to any individuals or linked with other readily accessible information that could be used to trace individuals.
Box's approach to data protection
Intelligent Content Management from Box provides one secure platform that protects your customer data with modifiable security solutions. Box's information governance features let you easily secure personal information of all kinds and determine best practices for your industry based on legal standards and recommendations.
As your company grows, Intelligent Content Management scales with you, giving you everything you need to manage large amounts of customer data while staying compliant with the most updated security rules and standards. You'll never fail to meet regulations with Box continuously maintaining your compliance. Our easy-to-use interface ensures all your employees keep up with security and compliance to protect customer information.
Storing and maintaining all your customers' personal information can be costly and time-consuming. Since Box is cloud-based, its retention management tools let you set a maintenance schedule and automatically delete files you no longer need.
Additional protection from Box Shield
Box Shield is a security program that can help you minimize risks with features such as alerts about potential threats and customizable PII data classification. Take your content to new security levels with labels that keep your files organized from the start — and machine-learning capabilities that identify issues in real time.
With Intelligent Content Management from Box, sharing sensitive information between parties is easy and secure. All authorized parties can access information through one user-friendly platform, integrating all your existing programs into one and eliminating the need to transfer data to other programs. Set rules in Box Shield that prevent unauthorized sharing of select documents for further protection.
Box continually updates its platform to comply with HIPAA and PII standards, so your organization's security measures always stay updated according to your specific industry standards.
Learn more about Box
With customers relying on you to keep their data safe, you need security that sets your organization apart. From payment card information to personal health information and other forms of identifiable data, Box empowers your teams to work efficiently and meet critical industry standards.
Whether you're looking to boost your data protection or you need an easier way to share files and collaborate with others on your team, Box can help.
If you want to know more about our range of services and solutions for your specific industry, contact us today for a personalized look at what we can do for you!
Learn more more about our range of services and solutions for your specific industry
**While we maintain our steadfast commitment to offering products and services with best-in-class privacy, security, and compliance, the information provided in this blogpost is not intended to constitute legal advice. We strongly encourage prospective and current customers to perform their own due diligence when assessing compliance with applicable laws.


