Data breaches among businesses and individuals are becoming increasingly more common. In 2020 alone, there were over 1,000 estimated instances of data breaches in the United States, with more than 155 million Americans affected by data exposure. While certain industries like healthcare, financial services, and government are considered prime cybersecurity targets, no business is safe from data breaches unless it takes the proper precautions.
This guide to understanding and preventing a data breach will explain what data leaks are, how they happen, and how to protect your content from them.
What is a data breach?
A data breach is a digital incident involving an unauthorized third party accessing sensitive information, either intentionally or unintentionally. When data falls into the wrong hands, it can put individuals or businesses at risk of financial or other damages. Third parties that obtain data can use it for various criminal reasons, including blackmail and financial fraud.
The underhanded nature of a data breach means the owner of the information is often not aware of their information being accessed or stolen until it’s too late. By the time the owner discovers the breach, the third party has already obtained the data and potentially used it to their advantage.
Data breaches are often the largest security threat businesses face. These incidents can result in reputational damage, lost clientele, exposed intellectual property, and legal liability. For individuals, data breaches can lead to financial hardship, including damaged credit scores or siphoned funds.
Data leaks vs. data breaches
Data breach and data leak are two terms used interchangeably along with a third term — data spill. Typically, when using the term data breach, most people are referring to theft, loss, or otherwise unauthorized access to sensitive information. A breach can compromise the integrity or confidentiality of data.
Data breaches are deliberate, strategic, and well-organized, often involving extensive research on the attacker’s part to discover a specific target’s unique vulnerabilities. Attackers often choose a target for the particular type of information they possess.
A data leak or data spill typically refers to a far less bold event, whereby information is exposed to a third party inadvertently or due to negligence on the owner’s part. A data leak doesn’t involve a devised attack, but may instead exploit some existing security weakness or capitalize on the mishandling of information. Whether data leakage is accidental or intentional, the result is the same: Sensitive information is compromised.
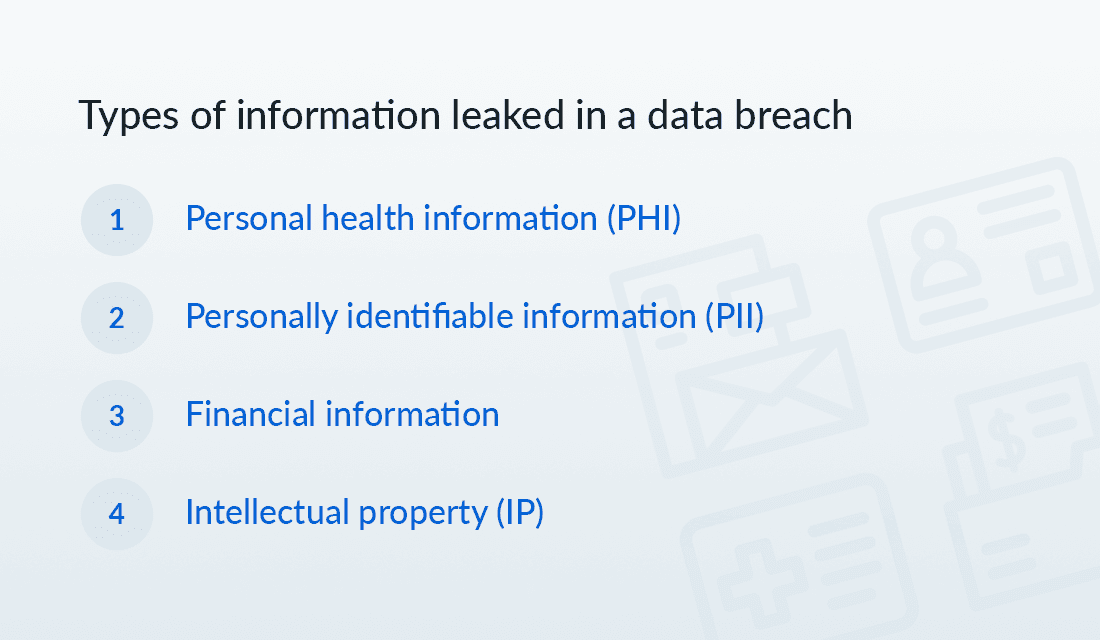
Types of information leaked in a data breach
Data breaches often target a specific industry, business, or individual for the type of information they possess. While data breaches may have a monetary motive, it’s not always financially related information that gets stolen. Businesses and individuals own various types of sensitive information that would be advantageous for a third party to obtain. Sensitive information can be used for extortion, blackmail, or other exploitative goals.
The type of information leaked in a data breach depends on who the target is and the purpose of the attack.
Below are four categories of information that may be compromised during a data breach or leak.
1. Personal health information
According to the Health Insurance Portability and Accountability Act (HIPAA), personal health information (PHI) constitutes “information that is created by a health care provider [that] relates to the past, present, or future physical or mental health or condition of any individual.”
PHI may include:
- Diagnoses and prescriptions
- Treatments, procedures, and surgeries
- Medical history and genetic information
- Primary health care provider information
2. Personally identifiable information
Personally identifiable information (PII) is any data that allows a third party to identify, contact, or locate you specifically.
PII can include:
- Full name, address, email, and phone number
- Date of birth and birthplace
- Social security number
- Passport, driver’s license, and vehicle plate numbers
- Usernames, passwords, and code words
3. Financial information
Financial information is any data that represents an individual or business’s monetary systems or status, including their credit and banking information, IRS data, and other accounts with financial access.
Financial information can include:
- Credit card information
- Banking numbers
- Invoices and bills
- Tax forms
- Financial statements
4. Intellectual property
Intellectual property represents anything that was created in the mind of an individual, such as a business or organization. Intellectual property is used by individuals and businesses to invent, build, design, or generally create something valuable.
Intellectual property can include:
- Patents, trademarks, symbols, and names
- Blueprints, plans, and designs
- Trade secrets
- Customer and supplier lists
- Contracts, licenses, and deals
- Business systems and processes
How does a data leak happen?
The process of leaking secured data occurs in several ways, depending on the nature of the incident. Broadly, data leaks can occur either intentionally or unintentionally, and they can happen from the inside or from an outside threat.
Below are three different ways that entities use data breach approaches to obtain compromised information.

1. Insider leaks
In one of the most deceptive forms of data leakage, individuals with insider information, such as employees, customers, or suppliers, may knowingly and willingly steal private data. Insiders may be motivated to steal company information for several reasons, including selling it on the black market for profit, starting their own company, or developing their own product.
A malicious insider leak can happen if someone intentionally misuses or abuses the authorizations or privileges they were given or if, because the employee has insider knowledge, they’re able to retrieve the information they otherwise aren’t authorized to access.
However, not all insider leaks are malicious. An employee may accidentally view their co-worker’s data, or they may unintentionally disclose information to an outsider by sending an email or chat to the wrong recipient. While the leaked information may never be used, it’s still considered compromised.
2. Inside or outside loss or theft
Not all data breaches involve the use of technology. Data can also be leaked or compromised due to physical theft. Whether it’s employees, customers, or suppliers, individuals may knowingly take devices, paperwork, or other physical objects that contain data. This theft can also occur to individuals when their cell phones, laptops, or notebooks are stolen, or when their ATM cards are skimmed.
As with other forms of data leaks, sometimes the loss of physical information is not intentional. Employees or individuals may simply lose track of their devices or notebooks, which doesn’t necessarily result in compromised data being used.
3. Malicious outside criminals
A final category of data leaks occurs when an outsider intentionally and maliciously uses criminal tactics. Generally, there are three categories of approaches to criminally obtaining secure data from the outside, each with varying degrees of maliciousness: phishing, malware, and brute force attacks.
Phishing
In phishing schemes, crooks use social engineering to devise a seemingly harmless situation that mimics a real-life interaction between people. Attackers pretend to be parties that you may naturally trust in order to persuade you to hand over sensitive information. Phishing often occurs via email.
Malware
In malware attacks, the miscreants exploit your system’s security weaknesses, inserting their programs into your system to spy on your behavior and retrieve your information. Malware is an invasive and insidious data breach approach that’s almost always undetectable by the target.
Brute force attacks
Brute force attacks occur when hackers use tools to find your passwords. Attackers may use a combination of malware and their own software to hijack your device and lock you out while they guess your passwords. These attacks can occur within a matter of seconds, depending on the strength of your passwords.
Data breach cycle: How hacks happen
Data breaches are cyclic in nature. Once the breach is initiated, it’s a matter of time before the target eventually discovers it. The target can learn how to better protect their information moving forward by learning the types of data that were compromised during the breach or leak.
Below are the five stages of the data breach cycle.

1. Vulnerabilities identified
A data breach starts when the attacker or leaker discovers a weak point from where they can obtain information. Depending on the nature of the breach, the attacker may conduct in-depth reconnaissance on a particular target, or they may capitalize on an unexpected or unplanned opportunity.
If the breach is malicious in intent, then the attacker typically seeks out the best point of entry into their target’s system. In elaborate schemes, the attacker may gather detailed intelligence on their target, including employee or manager roles at the company, what they post on social media, and any other publicly available information.
2. Strategy developed
The attacker creates an overall strategy based on the information they want. Their method may involve specific emails or communications used in phishing schemes, including setting up scam pages to mimic the company’s website. The strategy often involves using tools, such as malware or spyware, to infect the target’s system.
Criminal hackers are known to congregate on the deep and dark web, where they share strategies and identify targets. Becoming aware of the common strategies and approaches that criminal hackers use is the best way to identify these attacks before you fall prey to them.
3. Breach carried out
With a detailed profile and a strategy in place, attackers execute the plan to breach the target’s system. If the attack is successful, the culprit gains entry and locates the information they want. Depending on the type of data they seek, the attacker may need to conduct a deep dive and create disruptions to buy time. In this stage of the cycle, the criminals often use command-and-control tools to give them long-term power over the system.
Data breach tools are becoming increasingly more sophisticated, with many criminal groups now using programs that make it appear to security analysts that everything is fine even while a breach is ongoing.
4. Information stolen and sold
In malicious data breaches, attackers typically have an objective. Usually, the end goal is either to obtain data they can monetize on the black market or to destroy the target’s system. Sometimes, it’s both.
Once attackers have acquired the information, they may sell it on the dark web to buyers in search of copyrighted, classified, or financial data. Paste sites are websites where criminal hackers publish stolen data, making it publicly available. Alternatively, the hacker may contact the target to inform them of the compromised data, holding it ransom. These kinds of attacks can sometimes be politically motivated.
5. Breach discovered
Eventually, the target will discover the breach. According to IBM’s 2020 Cost of a Data Breach Report, the average time it took for a target to discover and contain a breach was 280 days. The longer a data breach goes undetected, the more damage the attackers can do.
Upon discovery, targets must gather information on the source of the attack, how it occurred, for how long, and what data was compromised. During the post-breach stage, targets decide which new security measures to implement moving forward, as well as how to support their customers or other compromised entities. How quickly and effectively a target responds to a discovered breach can significantly impact its reputation.

Data leak prevention
Businesses and individuals can prevent data leakage by conducting due diligence and taking the time to implement known data leak prevention tactics.
Below are a few best practices to follow to prevent data leakage.
Use unique and strong passwords
According to a 2019 survey by Google and Harris Poll on internet users, 52% reuse the same password across multiple different accounts. Reusing passwords is one of the primary ways that hackers are able to do as much damage as they can. Once they guess one password, they reuse that code or variations of it to gain access to multiple systems.
To prevent data leaks, users should always use unique passwords across different accounts. These passwords should also be strong. The longer a password, the stronger it is. Strong passwords contain both upper and lowercase letters, as well as a combination of numbers and symbols. Most people are worried about forgetting their passwords, so using a password manager can help encourage the use of unique options.
Use two-factor authentication
Two-factor authentication (2FA) is a login protocol that networks follow to protect user privacy. Cyberattacks are becoming increasingly more common, so 2FA is a critical security measure for businesses and organizations to protect their data from leaks. Two-factor authentication means that networks require users to enter their password, the first factor, as well as a second verification whenever logging in.
The second verification confirms that the person accessing the account is who they say they are. The user must respond to a verification prompt, typically involving a secret question or a code validation sent by email or text, to verify their identity. Two-factor authentication adds an additional layer of security that deters and prevents data leaks.
Conduct vulnerability assessments
Companies that access and store user information must take necessary steps to secure customer data, including ongoing assessments of their security systems. Security analysts look for vulnerabilities in their systems and determine the best approach for closing these gaps during assessments.
Likewise, individuals can also conduct vulnerability assessments for their personal data. There are many resources individuals can use to assess their digital privacy and security habits. Assessments usually prescribe actions individuals can take to strengthen their data security, including regular security updates, password changes, and other protection measures. Individuals can also routinely check their credit reports and monitor their accounts for suspicious activity.
Provide training and education
One of the best proactive measures businesses can take to prevent information leaks is to educate employees on data safety practices. Helping workers become aware of some of the common or possible phishing scams can help staff recognize socially engineered attacks.
Businesses should develop in-house protocols on how to handle suspicious activity, including who to report it to and how to proceed with using devices after a threat is suspected. Ongoing training can help businesses stay ahead of some of the latest attack strategies and tools that hackers use to infiltrate their targets’ systems.
Use secure and encrypted software programs and tools
Both businesses and individuals use a growing number of SaaS programs, apps, and other accounts that require password-protected logins. According to one report, the average small business uses 102 different SaaS apps, while enterprise-level businesses use an average of 288.
Businesses that store sensitive information regarding their employees, customers, suppliers, or other private data should use highly secure software programs and tools. Using encrypted SaaS programs allows businesses to demonstrate they are being proactive in preventing data breaches. When working with third-party software providers that offer high levels of data encryption and security, businesses can rest assured they will be compliant with any pertinent industry and government regulations.
How can you recover if your data is exposed in a data breach?
The first step for any business or individual to take when they discover a data breach is to find out what type of information was stolen. Then, they can alert the relevant institutions and parties who are affected by the breach.
For businesses, the following steps can help teams recover after a data breach:
- Having staff and customers change and strengthen passwords
- Patching and updating software if a new version is available
- Upgrading devices if a manufacturer no longer supports required software
- Requiring employees to only use business devices on a secured network
- Conducting a thorough cybersecurity audit
For individuals, taking the following precautions can help you recover from and prevent a future data leak:
- Reviewing account histories and reporting suspicious activity to the service provider and local police
- Signing up for monthly credit reporting to be alerted to potential identity theft
- Updating and strengthening passwords
- Using a different password for each online account
- Storing login information in a secure password manager
While businesses are required by law to report personal information data breaches to the police, individuals can also report identity theft to local authorities to assist in the collective effort to catch data thieves and prevent future instances.
How Box helps prevent data leaks
Box, the leading Intelligent Content Management platform, takes data protection very seriously. Get the productivity and workflow features you need without compromising security, and take the necessary steps to prevent a data leak, with Box.
Box helps you protect your data from leaks and breaches by providing security features. Some of the tools we use to help prevent data leaks include:
- File encryption through built-in controls that ensure strong user authentication
- Security protocols that help you meet compliance and governance criteria
- Intelligent threat-detection technology that uses machine learning
- In-depth visibility with audit logs and admin reporting tools
Learn more about how to prevent data loss with enhanced security from Box.
Learn more about what Box has to offer
Learn more about what Box has to offer
Built-in security and compliance features are only one aspect of what Box has to offer. Intelligent Content Management is our core offering, providing various tools to help businesses streamline their workflows and collaborate with teams in real time. Box has over 1,500 app integrations, so we can become your central operating hub, helping you and your team achieve higher productivity and more efficient operations.
Find out why over 100,000 organizations trust Box with their content and data storage needs. Discover all that Box has to offer. To learn more about data protection, contact us today.
**While we maintain our steadfast commitment to offering products and services with best-in-class privacy, security, and compliance, the information provided in this blogpost is not intended to constitute legal advice. We strongly encourage prospective and current customers to perform their own due diligence when assessing compliance with applicable laws.


