Information security and information privacy are increasingly high priorities for many companies. Breaches can be devastating for companies and consumers, in terms of both financial costs and business and personal disruption. More than 40 million Americans fell victim to health data breaches in 2019 — a staggering increase from 14 million affected in 2018.
Information security and information privacy are similar topics, so they often get lumped together or confused. Still, they are not the same thing, and they require different approaches if companies want to ensure effective protocols in both of these areas.
In this article, we cover the differences between data privacy and data security, explain why those differences matter, and offer some best practices for your company's approach to these critical topics.
What is information security?
Information security, or infosec, refers to the practices businesses use to protect information and infrastructure from unauthorized access and attacks.
Many companies implement comprehensive, detailed information security policies to keep their data, programs, and networks secure. Basic information security measures include encrypting data, installing firewalls, and using anti-virus or anti-malware protection to thwart cyberattacks. Information security measures also protect data as it’s stored, processed, and transmitted — essentially, throughout every step of its use.
Your data's security can become compromised in many ways, from phishing emails and malware hidden in website popups to keylogging programs and outright attacks from malicious actors. Your data could also be compromised if an employee provides data access to an unauthorized user. Business information security programs work to mitigate these threats and keep information systems safe.

Why is information security important for businesses?
Your company needs to keep your organizational data and systems secure for several reasons.
Maintaining operations and functionality: Many businesses rely heavily on their data and informational infrastructure to function. If hackers compromise your information, programs, or networks, your business operations could come to a standstill. You might get compromised networks up and running again relatively easily, but recovering valuable information could be another matter. This point becomes particularly crucial in mission-critical industries where even a brief system downtime could severely compromise operations.
Forestalling financial losses: Financial losses from security breaches are often severe. The average cost of a data security breach in the United States is $8.19 million, and in health care, the average cost is $15 million. Effective information security protocols help prevent these staggering losses.
Maintaining data confidentiality: Some information should not go beyond a few trusted individuals. Your company likely needs to keep its trade secrets and other confidential information secure to ensure profitability.
Upholding regulatory and ethical standards: Though information security does not receive stringent overarching regulation in the United States, certain laws do apply, especially in health care and education. Quality information security practices help you comply with the law and allow you to uphold ethical standards and industry best practices while demonstrating integrity and leadership in your field.
A company that wishes to bolster its information security should take the following steps:
- Determine what federal regulations, state laws, or industry best practices will govern your company's approach to information security
- Develop a rigorous, comprehensive information security policy for the entire organization
- Determine which employees have access to what data and systems under the policy
- Train employees on how to comply with the terms of the policy
- Reevaluate your approach as needed and adjust it to better address more sophisticated threats
What is information privacy?
Information privacy refers to control over individuals' personal data, such as personally identifying information (PII) or personal health information (PHI). In the United States and many other countries, these types of personal information receive legal protections. Consumers have the right to say how companies manage, share, and dispose of that information.
Think about the privacy policy a consumer must agree to while registering for an online account or downloading a mobile phone app, for example. In the privacy policy, the company lays out what type of information it will gather from consumers, how it intends to use this data, and what other entities it can and cannot share the data with.
Information privacy sometimes, though not always, overlaps with information security because sensitive user information can also be organizational data that requires security protections.

Why is information privacy important for businesses? Your company needs to ensure client data privacy for a few different reasons:
Maintaining regulatory compliance: Your organization needs to provide robust information privacy protections to comply with various laws and regulations. Your company should stay apprised of the applicable regulations governing data privacy for your operations and implement policies that comply with them.
Protecting customers: Your company should also ensure data privacy to avoid harming your clients. In the worst-case scenario, a malicious actor could steal client identities and cost your customers thousands of dollars. Keeping your clients' data out of unauthorized hands also protects consumers from harassment and intrusions and gives them peace of mind about their private information's safety.
Boosting consumer confidence: The way you handle sensitive consumer information will also affect the public opinion of your company. Navigating data privacy with confidence proves your reliability and trustworthiness to your clients and potential clients. It may well earn you substantial business and brand loyalty.
Avoiding financial losses: Consumers generally feel the direct economic impacts of data breaches most keenly. Still, your company could take a hit as well. Failing to comply with information privacy laws might earn your business hefty fines.
A company that wishes to set up an information privacy program will need to take steps such as these:
- Determine the level of privacy currently afforded through the company's policies
- Research the regulatory privacy standards the business must meet
- Learn about the privacy protection options available
- Confirm that these options will work within established organizational frameworks
- Train employees on how to handle consumer data according to these rules and in compliance with the law
- Manage consumer data according to the chosen protection options

The essential difference between privacy and security is that information security focuses on data and infrastructure, while information privacy focuses on people and their protected information. Information security protects a company's content and business objectives from threats and attacks, while information privacy respects consumer rights and keeps customer data secure.
A business organization's privacy program protects individual clients' personal information. On the other hand, its information security program protects all the organization's digital assets, from data, programs, and systems to networks and infrastructure.
One useful analogy for thinking about information security vs. privacy is that of a window in your living room. Having thick, resistant glass in the window and installing heavy iron bars on the outside are security measures. These features protect you from potential intrusions. Hanging curtains over your window gives you privacy by preventing passersby in the street from seeing in.
How does information security intersect with information privacy?
Some, though not all, information security practices also relate to information privacy. For instance, if a company has safeguards to encrypt and protect its data, the encryption keeps the data secure from threats, and it also keeps the data private. However, firewalls that prevent viruses from entering the company network or policies that prevent users from sharing trade secrets are unlikely to affect consumer data privacy directly.
Businesses often use information security and information privacy protections simultaneously. Think about a hospital that handles sensitive PHI. As facility personnel work with the PHI, they use secure systems rather than emailing about sensitive matters using their personal, unsecured email accounts. This step is an example of information security because it involves data protection using a secure system to thwart intrusions.
Employees at the hospital might also take more general steps to limit access to private patient health records. They might grant access only to authorized personnel such as the doctors and nurses on a patient's care team. They might also stipulate that employees may access patient information only during regular business hours unless an emergency occurs. Taking these steps allows the staff members to respect patient privacy as well as ensuring data security.

Here are a few more examples of how information security and privacy interact:
Effective security and privacy: Imagine that your company obtains consumer data and keeps it safe from unauthorized access. You provide both information security and information privacy.
Effective security but compromised privacy: Now imagine that your company obtains customer information and sells it to a third party in violation of your consumer privacy agreement. No intrusion or unauthorized breach of company security measures has occurred. However, the company has compromised the privacy of the information by sharing it with others without permission.
Compromised security but unbreached privacy: Now, suppose that a hacker breaches your company's firewall but merely interferes with some system operations instead of capturing valuable client data. Your security has been compromised, but personal customer information remains private.
Compromised privacy and security: Finally, imagine a cyberattack exploits your company's security weakness. The intruders gain access to protected personal customer information. This situation illustrates compromised security since the attackers broke through your defenses, and it illustrates compromised privacy because the hackers obtained data that should have remained private.
One of the main lessons in these examples is that it is easy to have security without privacy, but relatively difficult to have privacy without security. A company might knowingly pass along protected information without breaching its security protections. It's rarer for a business to experience an information security breach while somehow maintaining consumer data privacy. A targeted breach that leaves consumer data untouched is likely to be rare. It would occur primarily if the malicious actors executing the attack somehow made a mistake.
Many companies find that having a privacy protection program is impractical without also having an information security program. Without an information security program that includes stringent access controls, for instance, your company could soon lose clients' personal data to malicious actors who gain unauthorized access to the network. You would also then likely be violating information privacy laws.
Direct comparisons of information privacy vs. security
Let's look at some specific approaches to information security and information privacy.
Legislation vs. best practices
Information privacy has legal protections in many cases, especially across North America and Europe. Information security, on the other hand, has gained fewer legal protections. In the United States, the field has fewer overarching regulations, though individual states may have their own laws. The rules that do exist tend to focus on the legality and illegality of the use of industrial secrets, as well as on government information protection.The field of information security tends to use best practices for guidance in the absence of legal requirements. For instance, the rules in place for the payment card industry (PCI) do not come from local or federal laws. They are guidelines that financial institutions have put in place to ensure consistent data protection.
Procedures for information security and privacy breaches
Laws do, however, define the procedures for handling information security breaches and information privacy breaches. Your company must report any breaches or unauthorized disclosures of your clients' personal information to the appropriate authorities if your company operates in a country with laws governing information privacy breaches. If an information security breach occurs, you may choose to handle the matter internally, depending on the situation.
Personal health information

Personal health information (PHI) receives more legislative privacy protections than many other types of personal data.
General personal data is usually narrowly defined as information that could identify a person. It includes information such as an individual's full name, birth date, address, and social security number. On the other hand, PHI is information related to a person's medical conditions, doctor visits, and treatments. It receives more stringent protections than regular personal data. The law requires the person to whom the PHI applies to give explicit consent to every use, disclosure, and disposal of the information.
Deterrence and prevention
Many information security measures aim to deter and prevent malicious attacks from outside a company's network. These measures also attempt to prevent people within the organization from leaking confidential information to individuals outside the network or unauthorized individuals within the network.
Deterrence and prevention measures may also apply to information privacy, but they often apply in a more limited sense. Though companies want to prevent unauthorized privacy disclosures, these disclosures have less bearing on the company's internal operations and risks and may receive fewer deterrence and protection measures if resources are stretched thin.
Common issues in information privacy vs. security

The areas of information security and information privacy generally deal with different types of threats that businesses must remain alert for. Some of the most common risks and challenges in information security include the following:
- Phishing
- Malware
- Ransomware
- Data breaches
- Insider threats
Information privacy deals more frequently with threats affecting personal information, whether it is digital or not. Below are some of the most common concerns:
- Inadequate data anonymization
- Insufficient data protection
- Use or disposal of data without consumer consent
- Unauthorized data access
- Data sales to third- and fourth-party vendors without consent
Core principles for ensuring information security

Your business will likely want to focus on a few core principles as it puts protective measures in place. Three of the main principles in information security are those found in the CIA triad:
Confidentiality: This principle refers to restricting sensitive information assets to authorized users only. Your company can ensure the confidentiality of its information by implementing strict access controls and protective barriers against malicious actors.
Integrity: Your business should also ensure the integrity of its data. Regardless of the security protections your company puts in place, the data should remain intact, complete, and accurate. Preserving the data correctly keeps it usable while still secure.
Availability: Your business data should remain available to authorized users even with stringent security measures in place. This principle enables your company to strike an appropriate balance between protecting data and maintaining its usefulness within the organization.
Core principles for ensuring data privacy

When your business focuses on information privacy, it may choose to strive instead toward other fundamental principles such as:
Anonymity: Your company should try to anonymize consumer data as much as possible. Consider how you can collect useful survey data in aggregate, for instance, while eliminating identifying information from your records.
Notice and awareness: Notify your customers of the data you plan to collect and how you plan to use that data. On your website, inform your visitors if you use cookies to track activity. In person, make your clients aware of who will and will not have access to their personal information.
Choice and consent: Your customers should also be able to choose whether or not to consent to your proposed use of their personal data. Give them a clear way to opt out of your services if they do not want you to gather and use their information.
Access and participation: This concept refers to giving your consumers access to their own data and allowing them to correct it if it is incorrect. This principle often requires you to authenticate information before you use it. Offering access and participation helps your company avoid using and distributing inaccurate personal information about your clients.
Integrity and security: This principle overlaps a bit with the core objectives of information security measures. Your company should take every precaution possible to keep personal client data intact and secure. Limit access to personal data, protect against data loss and unauthorized disclosures, and destroy data securely once you no longer need it. These measures keep private data from falling into unauthorized hands.
Enforcement and redress: This principle requires a mechanism to enforce compliance with information privacy laws and penalize non-compliance. Your industry, for instance, may impose penalties if authorities discover non-compliance in your organization. Your consumers should also be able to seek redress if they learn you have been sharing their information without their consent.
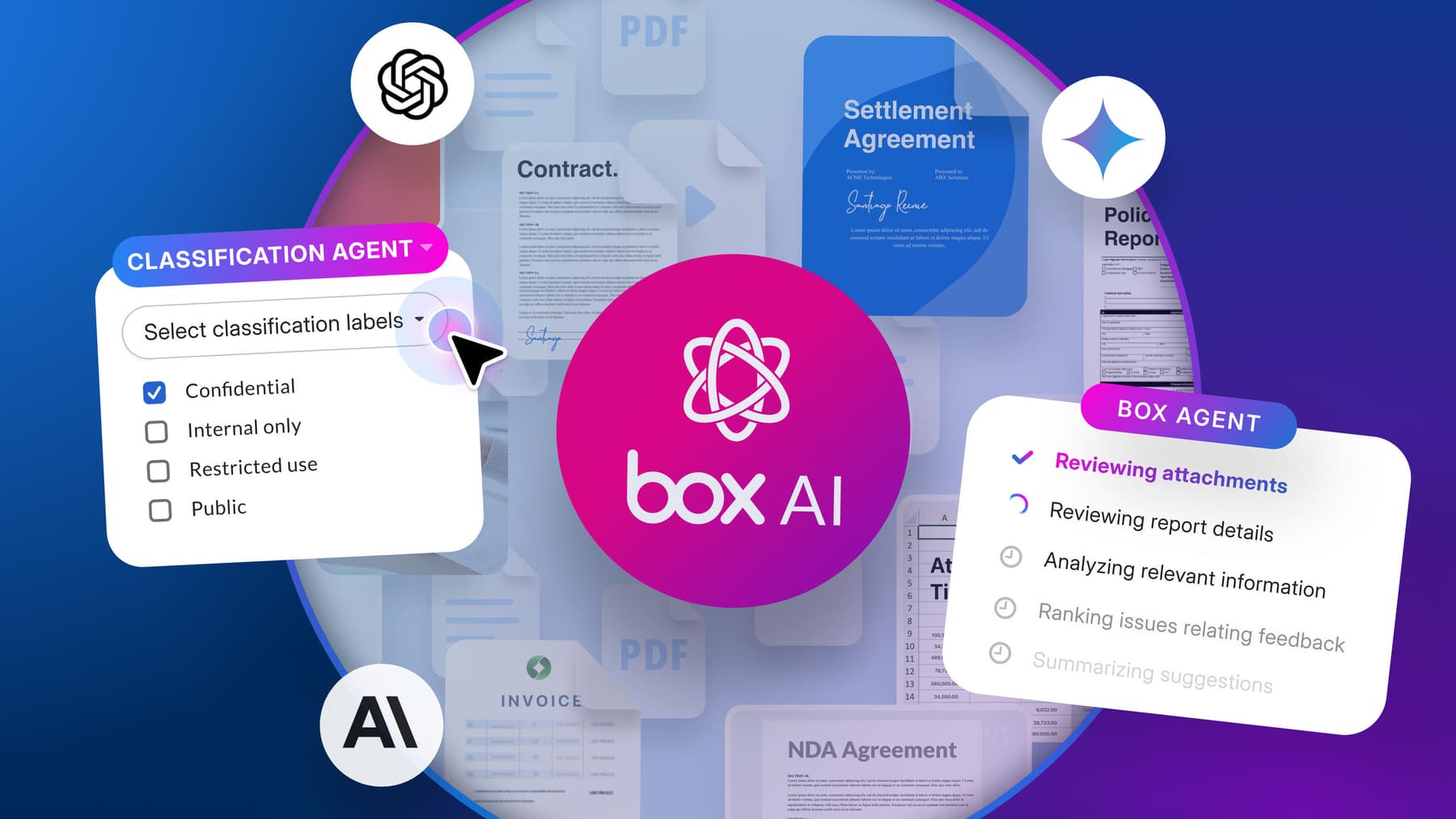
Protect your business with security and compliance from Box
When you need to ensure information security and privacy in your business operations, Box is here to help with security and compliance solutions. We provide services that optimize information sharing and collaboration while maintaining data privacy and security.
We place a great deal of emphasis on both privacy and security. Features include:
- 6 methods for native classification
- ML-powered auto-classification of PII, PHI, and custom terms in content
- Granular permissions and strong user authentication
- Every file encrypted using AES 256-bit encryption
- Simplified governance and compliance to avoid fines and meet the most demanding global compliance and privacy requirements
- The ability to monitor how work happens inside and outside your company, with insights and complete audit trails, along with machine learning to defend against threats
Box enterprise-grade security and compliance management solutions give you an intelligent, cloud-native approach to security and compliance. That way, your business has the most sophisticated tools available to bolster defenses and deter threats. Our systems are also easy to integrate with your existing IT infrastructure, so you can start boosting security without lengthy implementation periods or delays.
Get started with Box today, or contact us to learn more about upgrading your information security and privacy protections.
Protect your business with security and compliance from Box
**While we maintain our steadfast commitment to offering products and services with best-in-class privacy, security, and compliance, the information provided in this blogpost is not intended to constitute legal advice. We strongly encourage prospective and current customers to perform their own due diligence when assessing compliance with applicable laws.