FedRAMP Tailored is a relatively new streamlined process launched in August 2017. Most agencies and vendors don’t know much about this program. We’ll give a full breakdown of everything you need to know.
Key Insights
- What is FedRAMP Tailored?
- What is LI-SaaS?
- What Are The Requirements for LI-SaaS?
- How is LI-SaaS different than Low, Moderate, and High?
- What Products Are Best Suited For LI-SaaS?
- What’s The Most Effective Way to Leverage LI-SaaS?
- How Should Agencies Leverage LI-SaaS?
- Should Cloud Service Providers Get Authorized Under FedRAMP Tailored or FedRAMP?
- How Many LI-SaaS Products Have Received Authorization?
If you want to learn more about FedRAMP, be sure to check out our Ultimate FedRAMP Guide.
What is FedRAMP Tailored?
The PMO launched FedRAMP Tailored to speed up the adoption of cloud services in low risk use cases. This program streamlines the FedRAMP Authorization process by requiring fewer security controls.
By law, Agencies must use the NIST Risk Management Framework (RMF). The RMF forms the foundation for security baseline requirements. As you can imagine, the standards are quite high due to the sensitive data that federal agencies have. Both providers and Agencies spend significant investment to get authorization for a service.
CxOs, vendors and officials provided feedback that there need for a more streamlined process for low risk authorizations. Costs to satisfy the Low Impact baseline were still too high in certain cases. An easier authorization path would lower certification costs for vendors. It would also reduce time, money, and effort for agencies.
Collaboration between the OMB, NIST, and the Joint Authorization Board (JAB) lead to the creation efforts. The original program was first available for public comment in February 2017. There were over 330 comments from the agencies, industry and partners. Finalized documentation came out in August 2017, officially establishing FedRAMP Tailored.
What is LI-SaaS?
LI-SaaS stands for Low-Impact Software-as-a-Service. It is a status created for the FedRAMP Tailored program. FedRAMP currently has three sets of baseline security requirements: Low, Moderate, and High. These categories come from FIPS 199 standards. LI-SaaS is a lightweight version of Low in terms of security baseline requirements.
This program allows a provider to focus only on relevant requirements. Low Impact baseline has 125 security controls that providers must satisfy. LI-SaaS is a subset of these. The vendor must document and assess at least 37 security controls. That number can rise up by 10-20 depending on the situation. Some controls are the responsibility of the federal government and do not apply. If the control or control enhancement does not directly impact the security of a cloud SaaS, then it also does not apply.
For the remaining security controls, the provider must attest that they satisfy them. The attestation does not need supporting documentation, which can save time.
What Are The Requirements for LI-SaaS?
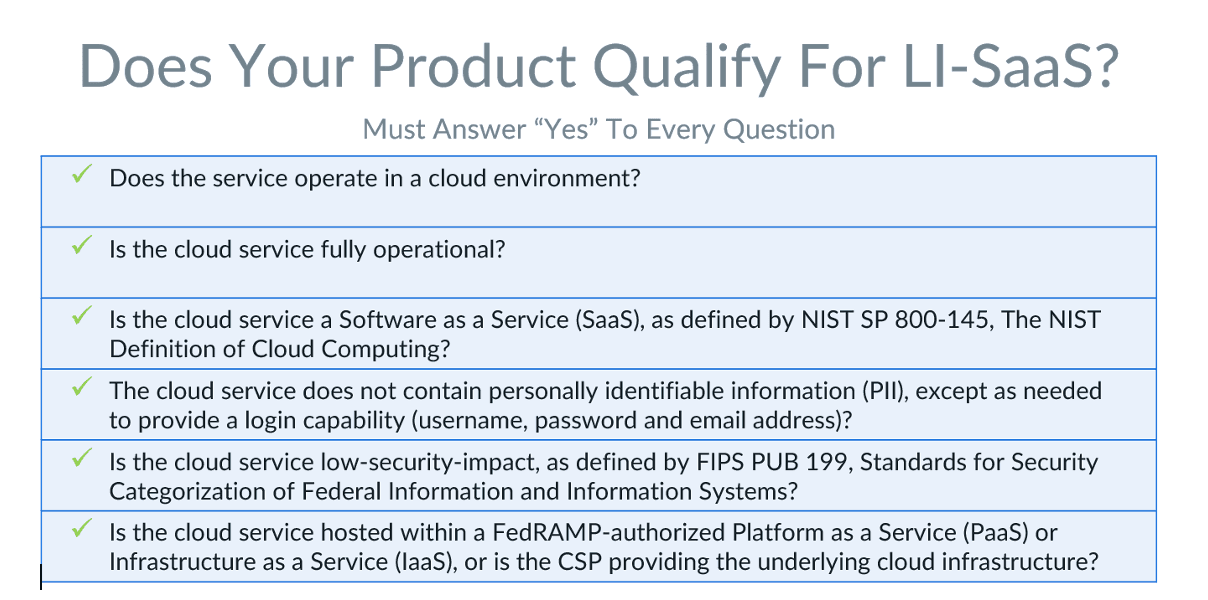
To be a FedRAMP Tailored LI-SaaS cloud service, the answer to all the following questions must be "yes":
- Does the service operate in a cloud environment?
- Is the cloud service fully operational?
- Is the cloud service a Software as a Service (SaaS), as defined by NIST SP 800-145, The NIST Definition of Cloud Computing?
- The cloud service does not contain personally identifiable information (PII), except as needed to provide a login capability (username, password and email address)?
- Is the cloud service low-security-impact, as defined by FIPS PUB 199, Standards for Security Categorization of Federal Information and Information Systems?
- Is the cloud service hosted within a FedRAMP-authorized Platform as a Service (PaaS) or Infrastructure as a Service (IaaS), or is the CSP providing the underlying cloud infrastructure?
- These tools could include collaboration tools, media editing software and project management applications.
There are some key nuances to understand. Only the necessary PII (personally identifiable information) allowed in the system is login credentials. PII can only be user name, email address, and password. Having any other PII disqualifies the system as a LI-SaaS. Even operating under this limitation is not best practice. Where possible, the vendor should not even use login PII. Rather, it should use an agency directory covered under an existing ATO and not store PII in its own system. An existing ATO with a higher baseline will provide a higher level of security guarding PII.
LI-SaaS systems must use an underlying FedRAMP Authorized PaaS or IaaS or use its own infrastructure. Leveraging an existing ATO allows the system to inherit the security controls. Using one’s own infrastructure requires an assessment of those controls. Some assessments may allow the use of certifications such as ISO-27001 or SOC 2, Type 2. In practice, it’s easiest to use existing authorized solutions to skip the assessment.
Although the FedRAMP Tailored Baseline provides a minimum set of security control requirements, each agency must still issue its own ATO. The agency must check for additional security controls required for compliance with agency-specific policies.
How is LI-SaaS different than Low, Moderate, and High Impact?
Impact refers to the severity an agency would experience if the system became compromised. LI-SaaS has the fewest number of security controls and can apply to limited low risk use cases. It is a modified, lightweight version of Low Impact. Low is suitable for limited negative impact, Medium is suitable for serious impact, and High is suitable for severe or catastrophic impact.
FedRAMP Tailored sets the LI-SaaS guidelines and security controls. This program streamlines the authorization process both for vendors and for agencies. Only the most relevant and applicable security controls need document and assessment. Vendors can meet the remaining controls by attesting that they meet the requirements and by inheriting certain underlying Authorized PaaS or IaaS controls.
FedRAMP controls the process for Low, Moderate and High Impact systems as required by law. Getting authorization is a much more involved process. There are significantly more security controls to document and assess.
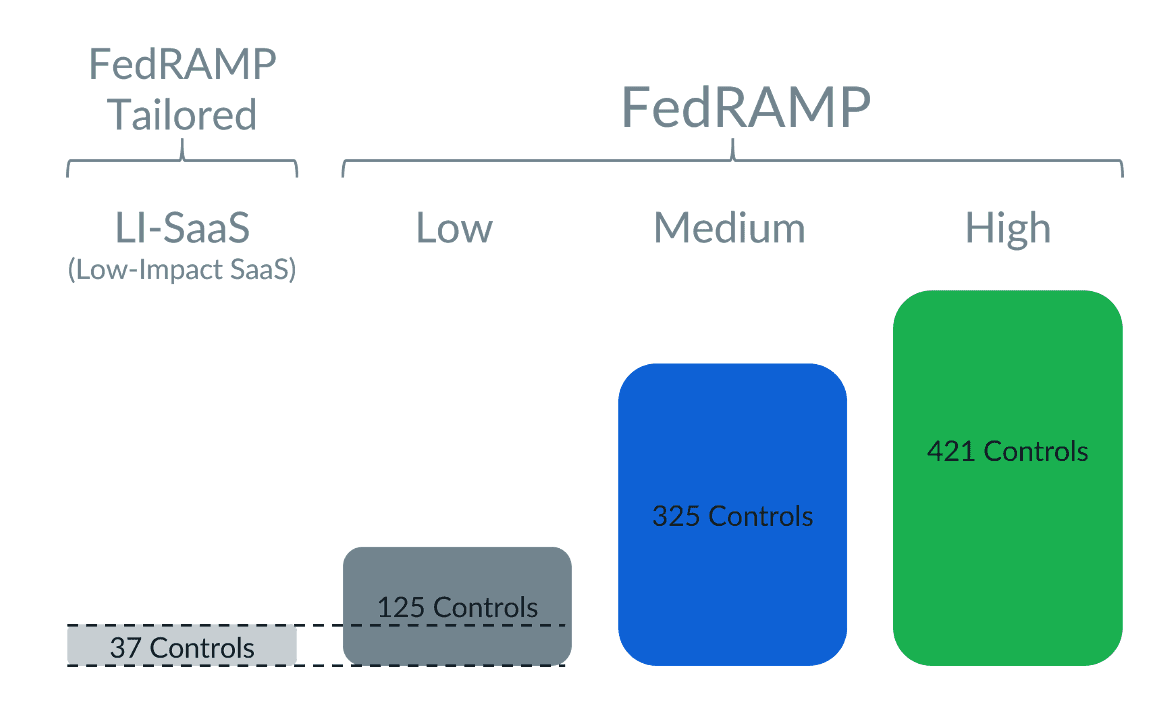
Here are the total security controls required for LI-SaaS, Low, Medium and High Impact:
- LI-SaaS: Minimum of 37, documented and assessed. Remaining security controls depend on situation or an attestation may apply.
- Low: 125
- Moderate Impact: 325
- High Impact: 421
What Products Are Best Suited For LI-SaaS?
LI-SaaS is only suited for situations that are low risk to the agency in the event of a compromise or failure. Here are some of the best products for LI-SaaS:
- Collaboration tools
- Project Management tools
- Tools for open source development
- Media editing tools such as image or video editors
- Public-facing website content management systems
- Training and education software
These products cannot contain any PII (personally identifiable information) other than login information. These system generally do not contain sensitive data that would be detrimental in the case of unauthorized access.
What’s The Most Effective Way to Deploy LI-SaaS?
The key to success is to leverage FedRAMP Authorized products. Remember that the basis of FedRAMP is to re-use certified products as much as possible. If one requires back-end cloud infrastructure, consider AWS or IBM Cloud For Government. If the LI-SaaS product deals with any content, files or documents, use Box For Government. Building upon existing products with accelerate adoption since the foundational elements are secure.
For example, the products below have secured FedRAMP Authorization and depend specifically on Box’s platform
- Broadcom: General Support Systems (GSS)
- Casepoint: Casepoint Government
- Cisco Systems: Webex for Government
- DocuSign: DocuSign Federal (eSignature, Gen, Negotiate)
- MDRC: SPROUT
- Palantir Technologies: Palantir Federal Cloud Service
- Palo Alto Networks: Palo Alto Networks Government Cloud Services - WildFire
How Should Agencies Leverage LI-SaaS?
Agencies should consider the following for LI-SaaS
- Determine if adopting cloud software is appropriate for the use case
- Assess if the impact and risk to the organization is low
- See if an existing FedRAMP Authorized product exists
- If no product is authorized, determine if the cost to issue an agency ATO justifies the benefits
Agencies should first assess the use cases and benefits of specific cloud products. SaaS products are often more cost efficient since they are much easier to manage than on premise software solutions. Most inertia comes from the cost of migrating to a new solution. Implementation costs can be high. Training people to use new software also requires time. But maintaining legacy solutions is almost never worth it.
The use cases must also be appropriate for a Low Impact categorization. If there is any possibility to have serious or severe negative risks in the event of a failure or compromise, then LI-SaaS is inappropriate. There also can’t be any PII data involved other than login information.
The easiest path to adoption is use an existing FedRAMP Authorized product. All product impact levels (LI-SaaS, Low, Moderate, High) satisfy the LI-SaaS security baselines. The Agency must still assess if the system fits the use case and issue its own ATO letter. But it is much easier than going through a full security assessment and authorization process.
If no Authorized product exists, then the Agency must determine if it’s worth it to work with a vendor to go through the FedRAMP Tailored process. They must commit to running a full process. But this process is much more streamlined than the traditional FedRAMP Process
Should Cloud Service Providers Get Authorized Under FedRAMP Tailored or FedRAMP?
The FedRAMP Tailored program lowers the barrier for cloud providers to sell to federal agencies. It’s an exciting path to access a large market opportunity. The downside is that LI-SaaS is only for low risk applications.
Vendors should work with agencies to find out the demand and use cases for their product. Then they should analyze the security needs. Those requirements will determine which impact level is suitable. LI-SaaS and Low impact authorizations must go through an Agency Authorization process. Moderate and High generally go through the JAB Authorization process. The JAB P-ATO process takes longer than the Agency ATO process. FedRAMP Tailored is specifically for LI-SaaS and must go through an Agency process. Low, Moderate and High authorizations must go through the traditional FedRAMP route.
In practice, vendors need to analyze the cost of going through each process. FedRAMP Tailored has a significantly more streamlined process. Some vendors can go through this process first as a stepping stone towards a higher level status. It can make future authorizations for a higher level easier. That is primarily due to already having met a subset of security controls. An added bonus is that if a vendor wants to go through a JAB P-ATO, the JAB prioritizes those with the highest chance of success. If a vendor has already obtained Authorized status, there’s confidence that it can be successful in another authorization.
Most vendors who choose to go through the traditional FedRAMP process must evaluate the time and investment required. 80% of vendors choose Moderate because it satisfies most use cases. The authorization timeline between Moderate and Low is the same. As a result, most vendors choose the Moderate path. Moderate has 2.6x the security controls required, so cloud providers must come prepared.
If cloud service providers are pursuing a Low, they should consider the FedRAMP Tailored program. Achieving LI-SaaS is much easier than Low. Otherwise, they should consider skipping Low and moving straight to Moderate given that that authorization timelines are similar.
How Many LI-SaaS Products Have Received Authorization?
As of April 2021, there are nearly 30 LI-SaaS FedRAMP Authorized applications launched since the program started in 2018. This is a promising new path for agencies and vendors to accelerate cloud adoption within the federal government. The streamlined and lower cost process is beneficial in limited low risk use cases.
Learn more about what Box has to offer
**While we maintain our steadfast commitment to offering products and services with best-in-class privacy, security, and compliance, the information provided in this blogpost is not intended to constitute legal advice. We strongly encourage prospective and current customers to perform their own due diligence when assessing compliance with applicable laws.