
HIPAA, formally known as the Health Insurance Portability and Accountability Act of 1996, is a collection of rules and standards for using, managing, storing, and sharing protected health information. PHI includes personally identifiable information, contact details, treatment plans, medication lists, financial information, care plan records, pictures, and more. Electronic PHI, called ePHI, refers to all digitally stored, accessed, or transmitted PHI, like information from online health portals and patient accounts.
Learn more about HIPAA security compliance, specific rules your organization should be aware of, and how to maintain security in your healthcare facility.Understanding HIPAA compliance

Understanding HIPAA compliance
HIPAA protects patients' sensitive information, including conversations and health insurance and billing information. The Office for Civil Rights and the Department of Health and Human Services enforce and regulate HIPAA. Legally, healthcare facilities and associated contractors and businesses must achieve and maintain HIPAA compliance.
Facilities that demonstrate compliance set the standard for healthcare organizations, since they have a patient-first attitude and approach PHI with privacy and care. Failure to achieve and maintain HIPAA compliance can result in costly fines, legal action, criminal penalties, and damage your organization's reputation for providing top patient care.
What is HIPAA compliance certification?
HIPAA certification is an optional training program your facility can participate in to learn more about becoming HIPAA compliant. Typically hosted by third-party experts, these programs leave you with extensive training and tools specific to your industry and site-specific needs. Earning HIPAA certification is not the same thing as being HIPAA compliant, but the resources you receive and tips you learn throughout your certification course may better prepare your facility for achieving or maintaining compliance.
Many organizations outsource certification training for a fresh, unbiased perspective on current operations and policies. These third-party experts save facilities the time and resources associated with assigning, delegating, onboarding, and training an internal specialist or committee.
Your facility can use your HIPAA certification to market your care for patients and the standard you hold yourself to.
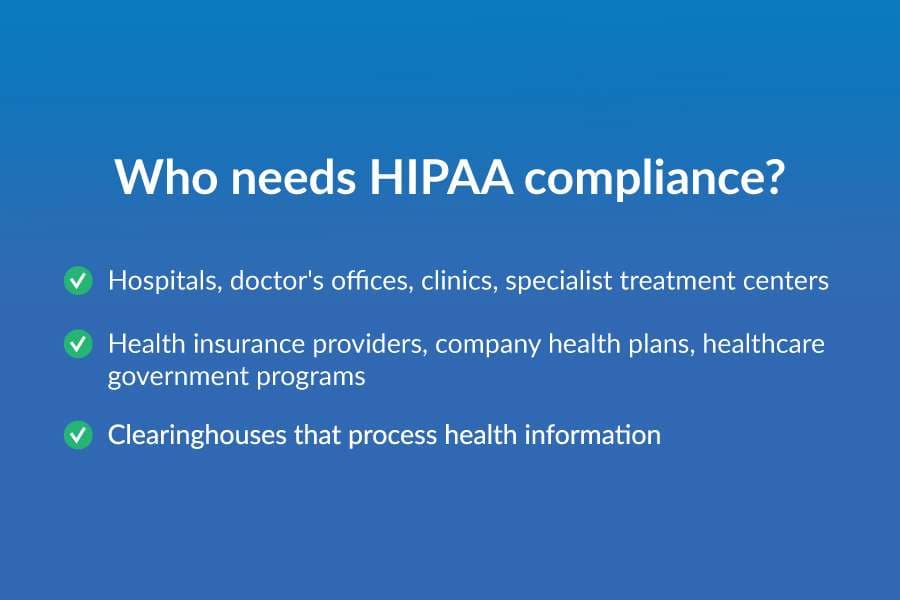
Who needs HIPAA compliance?
Organizations complying with HIPAA are called covered entities. Examples of healthcare organizations responsible for meeting HIPAA standards include:
- Hospitals, doctor's offices, clinics, specialist treatment centers
- Health insurance providers, company health plans, healthcare government programs
- Clearinghouses that process health information
Some organizations that may not always have an obligation to achieve HIPAA compliance are life insurance companies, workers' compensation facilitators, schools, and law enforcement.
HIPAA compliance also applies to each covered entity's business associates. Business associates are any contractors, subcontractors, and external experts that may have access to PHI. Typical business associates include lawyers, billing companies, accountants, and technical professionals. HIPAA-compliant facilities must ensure all business associates follow HIPAA practices to use and protect PHI and all related rules.

What are the HIPAA rules to know?
Since HIPAA's original enactment, the HHS has passed several rules to clarify and modify regulations and introduce new guidance to fit evolving technology and patient and facility needs.
HIPAA Privacy Rule
The HIPAA Privacy Rule protects PHI by imposing limits and specific conditions for how covered entities and business associates can use and disclose individual medical information. It encompasses several HIPAA regulations, including these examples:
- Patients have the right to request and inspect their PHI and request corrections if necessary
- Facilities require patient authorization for most disclosure
- Patients have a right for health providers to notify them regarding how they will use, share, and disclose information and can refuse some uses
- Facilities should make an effort to disclose the minimum amount of necessary PHI and no more
- Facilities can disclose some PHI without written consent, such as that necessary to facilitate treatment
The Privacy Rule applies to many typical medical forms, including the Notice of Privacy Practices, the Request for Restriction of Patient Healthcare Information, the Authorization for Use or Disclosure, and the Request for Access to Protected Health Information.
HIPAA Security Rule
The HIPAA Security Rule dictates regulations, standards, and procedures relating to all saved, accessible, and transmitted ePHI and paper PHI. It consists of three separate protection levels, including:
- Administrative security measures, like having a HIPAA compliance team or officer
- Technical security measures, like data encryption and user authentication
- Physical security measures, like locks and technical safeguards at physical locations in your facility
Covered entities should analyze their situation to determine the best way to enact each security method. Your facility should have a written policy of relevant privacy procedures and consider delegating a privacy officer to oversee compliance management and implementation. Be sure to identify which departments, employees, or business associates have access to specific parts of your ePHI — never grant access to a user unless the information is critical for patient care, management, or billing. The Security Rule also applies to all third-party business associates working with the covered entity.
HIPAA Breach Notification Rule
According to the Breach Notification Rule, covered entities must report any PHI security breach within a specific timeframe, depending on how many individuals it affected. The Breach Notification Rule also requires covered entities to publicly display large-scale breaches. The HHS defines a breach as any situation where an unauthorized party accesses or discloses PHI. Circumstances constitute a breach unless the covered entity can demonstrate a low probability of a significant rule violation by assessing:
- The nature and extent of the PHI accessed, including how much identifiable information was available
- The person or party who accessed the PHI and whether they acquired or viewed it
- How much the organization took steps to mitigate the risk of PHI access
Some breaches are an exception to the Notification Rule, such as:
- Those unintentional by a person acting under the authority of the covered entity or business associate
- Accidental PHI disclosure by one authorized person to another
- If the covered entity believes the unauthorized person wouldn't have retained the information if viewed
HITECH
The American Recovery and Reinvestment Act created the Health Information Technology for Economic and Clinical Health Act, or HITECH, to encourage healthcare facilities to start using electronic health records in place of, or in addition to, traditional paper records. The act incentivized using EHR and strengthened existing HIPAA provisions by bolstering the Privacy Rule and Security Rule for covered entities, business associates, and any relevant subcontractors.
All business associates must use the same HIPAA compliance as the covered entity under HITECH, with stricter penalties if neglected.
HIPAA Omnibus Rule
The HIPAA Omnibus Rule updated existing HIPAA and HITECH regulations to make business associates directly liable for any penalties or fines associated with noncompliance. It combined several existing rules into more cohesive standards, adding more detailed requirements for issuing data breach notifications and enforcing penalties. It included guidance for managing PHI and marketing, exchanging PHI for payment, and disclosing PHI to specific people or organizations.
The Omnibus Rule says organizations should modify privacy practices and internal practices to reflect updates and extend those adjustments to any Business Associates with access to PHI. It also heightened penalties for noncompliance — under Omnibus, fines and legal action vary based on how negligent they are and could cost companies hefty fees.

What does HIPAA compliance require?
Much of the language in HIPAA guidelines is intentionally vague because each facility, organization, and company plays a different role and has various needs, depending on multiple factors. A HIPAA compliance checklist and certification training program are excellent places to start, as they offer expert guidance for areas to consider and site-specific tips.
Self-audits and risk remediation
Every facility should conduct regular self-audits of all processes, business associates, technology, employees, training, and other administrative, technical, and physical factors. Facilities should also conduct an audit after any significant organizational change, like new staff or management, department relocation, process changes, new technology, or similar occurrences that alter how organizations access, store, and transmit PHI. Audits are a critical part of achieving HIPAA compliance, but also maintaining it.
Once you notice gaps, vulnerabilities, or existing issues in your self-audits, create a robust action plan to remediate those concerns and fix any violations. Be sure to document each step of the process, including the dates of all inspections and remediations, organizational goals, and other essential information. Always adjust existing policies and procedures, so the language and principles reflect your organizational changes and new HIPAA standards.
Employee training and education
HIPAA requires that every covered entity and related business associate conduct regular training for all employees who handle PHI, no matter their level or department. Conduct new training after every change to internal processes or HIPAA guidelines and during and after risk remediation.
Training should be thorough and customized to your facility's needs and concerns. Consider outsourcing some parts of this instruction to a third-party HIPAA compliance expert, who can provide an unbiased look at your current situation and make recommendations with valuable insight. Training sessions with employees should cover everything they need to know for handling patient PHI safely and securely. However, the law doesn't require employees to participate in any training sessions that don't apply to their role in your facility. For example, IT specialists won't typically attend special training for bedside PHI standards, but would need to be present for administrative PHI updates.
During training sessions, help your team understand the reason behind HIPAA compliance and how it benefits each patient and the organization as a whole. Understanding why each guideline exists is a helpful way to motivate staff to work hard to maintain strict standards each day. Be sure to include plenty of time for questions and feedback, and don't forget to document everything about the training, including when and where it took place, employees or departments present, subjects covered, and any management, leadership, or third-party experts in attendance.
Another part of maintaining HIPAA compliance is ensuring leadership and high-level team members stay informed about alterations to HIPAA policies and associated rules. Management should attend industry conferences, read industry materials, and stay abreast of federal and state changes.
Organized documentation
Accurate and up-to-date documentation is an essential part of achieving and maintaining HIPAA compliance. You should keep a record of every step of your facility's HIPAA journey, including — but not limited to — the following information:
- Certification materials
- Training sessions
- Third-party assistance
- Administrative forms
- Employment information
- Self-audits and reports
- Risk assessments
- Remediation plans
- Contingency and emergency plans
- Detailed logs and access lists
- PHI location documentation
- Business associate agreements
- Work desk and mobile workstation procedures
- Breach response plans
- Vendor agreements
- Physical security measures
- Employee handbook
This documentation will prove critical during self-audits, surprise audits, and investigations. It's also an easy way to track your team's year-to-year progress and leave instructions for new management or employees as your team evolves. If the HHS decides to audit your facility, you can use your documentation to demonstrate an existing effort to reach compliance if you're not already compliant. Store documentation in a safe, secure place and revise contents as needed. Examine documentation as part of your self-audits to determine areas of improvement and areas that need further addressing.
Incident response plan
Healthcare organizations saw an average of 1.76 security breaches each day in 2020. A security incident response plan details how your facility will address all possible risks. For PHI, this means unauthorized access or disclosure, ransomware attacks, data loss or theft, and hacking.
It's critical to note the difference between security instances and official security breaches. During a breach, there is either confirmation or reason to suspect an unauthorized person or party has accessed PHI. Security incidents are when someone may or may not have accessed or taken PHI, either intentionally or unintentionally. Incidents become breaches once anything has compromised unencrypted data. Covered entities must file reports during each breach or prove otherwise.
Penalties for breaches and severe incidents vary, but consider factors like incident security, steps to mitigate the violation and how long remediation took, who accessed the PHI, and other specific details surrounding the occurrence. An incident response plan demonstrates your facility's dedication to security and gives each employee or department clear, step-by-step instructions for approaching security incidents.
Your incident response plan should be in writing and detail the following:
- Steps for determining possible risks
- How you will evaluate an emergency or suspicious activity
- The escalation hierarchy for breaches or suspicious activity
- Steps to mitigate existing threats
- Which person or department is responsible for analyzing and remediating instances
- Steps for recovering lost PHI and other important files
- How you will inform affected patients or employees during security breaches or incidents
- How you will implement changes and adjust existing policies after any occurrences
- Your team's post-occurrence cleanup plan
Security incidents and breaches can result in hefty fines, criminal liability, and legal fees — a zero-tolerance policy against intentionally mishandled breaches is one way to keep your organization and patients safe.
Elements of effective HIPAA compliance
The HHS issued seven elements for effective HIPAA compliance:
- Have and implement written policies and standards of conduct for all key areas
- Designate a compliance team or officer to manage your organization's journey toward compliance, including audits and remediation
- Have ongoing, practical training and education for employees, leadership, and business associates
- Have a plan for effective communication with all relevant parties
- Have transparent internal monitoring and regular audits
- Enforce your standards with publicized disciplinary actions and zero-tolerance policies for misconduct
- Respond to offenses and security incidents quickly and take appropriate corrective action
Other helpful tips to achieve HIPAA compliance are to start at the top of your organization and make changes as you move down — employees will look to management for leadership and guidance. Take steps to install each team member with a patient-first mentality, stressing the importance of individual privacy and PHI protection. Never be afraid to seek outside help or third-party assistance if your organization struggles to identify or correct existing security concerns. Don't put off working toward or improving compliance — start implementing changes today.

HIPAA violations
Failing to adhere to HIPAA regulations can lead to legal action and costly penalties. In 2020, Premera Blue Cross paid a $6.85 million fine for a data breach affecting 10.4 million people, one of the highest HIPAA-related fines in the OCR's history. The largest single settlement was in 2018, when Anthem, Inc., paid $16 million for a health data breach affecting 79 million people. Extreme situations may even result in jail time.
Not all violations have the same consequences. Intention, existing compliance efforts, due diligence, and the breach in question each play a role in the severity of an organization's penalty:
- Tier 1 violations are typically accidental, or the facility is unaware of the breach, even after reasonable due diligence
- Tier 2 violations are more penalized, as it represents a violation that the facility should have known about with reasonable due diligence
- Tier 3 is when a facility wilfully neglects HIPAA compliance and corrects it within 30 days of discovering the issue
- Tier 4 is when a facility wilfully neglects HIPAA compliance and makes no effort to fix the issue within 30 days
Internal audits uncover most violations, but employees can self-report violations or report co-workers. Patients may also file a formal complaint, prompting an investigation.
HIPAA violations to watch for
Some common HIPAA violations include:
- Failure to conduct a thorough, facility-wide risk analysis or taking steps to remediate issues found
- Failure to use HIPAA-compliant contracts with vendors and business associates
- Delaying or neglecting to issue notification for data breaches
- Not prioritizing risk management and PHI protection
- Denying patients access to their health records or taking too long to permit access
- Disclosing PHI beyond the expiration for a patient's consent
- Failure to maintain PHI access logs
- Neglecting to implement PHI security on mobile workstations and portable devices
- Improper disposal of PHI and ePHI

How Box ensures HIPAA compliant data sharing
Box can help your facility meet and maintain HIPAA compliance. We sign a business associate agreement with all clients using our platform to store PHI, and a third-party auditor has verified our secure system to meet HIPAA requirements for data security. We update all products and policies to maintain this level of compliance.
Examples of HIPAA-compliant tools include:
- Encryption for stored and in-transit data
- Strict system access controls
- Reporting and audit trails for all account activities and users
- Highly restricted employee access to customer data files
- Employee training for top security and data management
While our team is happy to bolster your facility's HIPAA compliance with easy-to-use tools, your organization retains responsibility for configuring each service and product in a HIPAA-compliant manner and enforcing internal policies to meet those requirements.
Let Box help you meet HIPAA compliance requirements
Intelligent Content Management from Box can help you and your team stay HIPAA compliant while simplifying your everyday processes on a single, easy-to-use, intelligent platform. Intelligent Content Management includes tools for seamless mobile collaboration, HR onboarding, optimized workflows, and so much more, all backed by prioritized security and data privacy, so you can get work done with peace of mind.
Learn more about Box services and see what we can do for your facility today.
Let Box help you
**While we maintain our steadfast commitment to offering products and services with best-in-class privacy, security, and compliance, the information provided in this blogpost is not intended to constitute legal advice. We strongly encourage prospective and current customers to perform their own due diligence when assessing compliance with applicable laws.


