Almost half of all American consumers experienced financial identity theft in 2020, costing a total of $712.4 billion in the process. And that number is only going to continue growing, with experts predicting $721.3 billion to be lost to identity theft in 2021.
Identity theft is a significant concern for individual internet users, but also small, mid-size, and even large-scale businesses. Whether you're a medical professional, office manager, retail shopper, or anything in between, cybersecurity is an essential part of protecting yourself online.

What is identity theft?
Identity theft is when a person or entity uses you or your organization's information — including your name, contact information, financial accounts, social security number, and other details — without permission. They can use this information to open new lines of credit or accounts, steal tax refunds or government benefits, or rack up hefty shopping bills or criminal activity in your name.
Identity theft can happen in person. For example, someone can steal critical documents from your filing cabinet and assume your identity or gain access to your bank accounts by swiping your credit cards or checkbook. Although it's important to stay vigilant for physical threats, the internet has given cybercriminals more opportunities to seize unauthorized information than ever before.
Four common types of identity theft in 2020 were:
- Government benefits
- Credit card fraud
- Business and personal loans
- Tax fraud
Other types of fraud include employment-related theft, opening utility accounts, or using your credit report to sign a lease on a vehicle or home. The Federal Trade Commission (FTC) doesn't have any legal jurisdiction to prosecute these felonies, but they are an active part of reporting, preventing, identifying, and stopping identity theft. They work with law enforcement agencies to educate consumers and solve the growing crisis.
How are identities stolen?
Individuals and organizations rely on the internet for everything from financial management and business operations to sensitive communication and data storage. Technology is a valuable asset for productivity, organization, and even entertainment, making identity theft more accessible for the average cybercriminal.
Some common methods of online identity theft include communication schemes, malware infections, doxxing, and device swiping.
Phishing, smishing, and pharming schemes
Phishing, smishing, and pharming schemes are all methods of having your information taken through dishonest communication. Phishing is an email-based scam where cybercriminals pose as a trusted brand, company, or loved one so you will click a link or download an attachment, allowing access to your personal information. Pharming is similar to phishing but happens without a "lure" and secretly installs malicious code on your device. Smishing is the same as phishing but uses text messages instead of email.
Some ways to spot a potential scheme include:
- Unsolicited messages and phone calls
- High-pressure language, like "click now" or "act fast"
- Typos or grammatical errors throughout the message or website
- Claims of suspicious account activity with a click-through link
- Fake invoices
- Free coupons
- Generic greetings, like "Hello, Dear"
Always consider the sender before clicking links or downloading files — do you know them personally or have an existing account with them? Does the context of their message make sense? If so, visit their website by closing the message or hanging up the phone and contacting them through a known, trusted source.
Malware, spyware, and ransomware
Ransomware and spyware are both types of malware — "malicious software" — that threaten your device and network security. Ransomware comes with an attached threat for information or money and typically targets businesses. Spyware files can infiltrate, monitor, and even control individual computers while harvesting data from your keystrokes and redirecting you toward harmful sites.
Signs you might be dealing with one of these threats include:
- Lagging performance or unexpected device crashes
- Known worms, viruses, or Trojans
- Excessive popups and ads while browsing
- Threatening messages
Protect yourself against these threats with antivirus software, security suites, and up-to-date security practices.
Doxxing
Doxxing is when an unauthorized person or entity collects personal information about an individual, including private photos, messages, contacts, locations, files, and addresses, and publishes it in an attempt to shame or harass the victim. They can use the information they collect to steal your identity or control your online image in a way that also jeopardizes your safety and right to privacy.
Protect yourself against doxxing by keeping social profiles private, removing locations from online accounts, only connecting with people you know, and using a virtual private network (VPN) in public spaces.
Discarded devices
Discarded smartphones, laptops, wearables, and tablets are full of valuable information, including banking apps, contact information, and login information. Device theft and improper device disposal made up more than half of 2020's reported physical attacks of identity theft.
Never toss an unwanted device into the trash without factory resetting it and wiping all data from the system. Recycling is the best option since it will also get a second life once you've cleared your information from it and taken it to an e-waste processing center.
How to protect yourself on the internet
Identity theft can be an overwhelming prospect, but there are several steps you can take right now to protect yourself and your organization from unauthorized access.

Manage passwords and devices
Choose strong passwords for your online accounts that combine uppercase and lowercase letters, numbers, and symbols, and never leave login information where someone else could access it. Vary your passwords across websites and keep them updated every few months for added protection.
If you fill out security questions, make sure they are challenging questions only you would know the answer to. Multifactor authentication — where logging into a device requires multiple forms, like both a pin code and a password — is the safest option, especially when combined with biometric unlock features, like fingerprint scanning and facial recognition.
Protect your privacy online by avoiding these common passwords and similar variations, like "password" or "password123," which cybercriminals have no trouble guessing:
- 1234
- 12345
- 123456
- [BLANK]
- system
- admin
- enable
Support password strength by keeping your devices up to date with the latest operating systems and security patches. Most smartphones and laptops let you set your system to update automatically so you're always up to date without having to remember to download or install anything.
Secure your network
Wi-Fi networks work by emitting signals through the air that let you connect your devices — including phones, digital assistants, smart TVs, appliances, and computers— to the internet. If you're not careful, people waiting within range of your network can access important information, spy on your activities, or access your personal accounts. They can also use your internet network to commit online crimes, like fraud or theft, which then traces back to your place of business.
Protect your network with these tips:
- Lock your Wi-Fi network and require a strong, unique password that you change often
- Use a mobile internet app to monitor the devices that connect to your network and block any you don't recognize
- Encrypt your business network with WPA2 or WPA3 encryption
- Change your wireless router's default Wi-Fi and router admin passwords
- Turn off remote management features
- Set up a guest network for visitors to access while at your facility
- Name your network something unique but not easily identifiable or easy to target
- Install security suites and antivirus software on all devices and upgrade to premium protection when possible

Monitor your credit
Your credit report summarizes all of your personal credit history, like past purchases, open accounts, existing debt, and account inquiries. A good credit score plays a significant role when buying a home, applying for a loan, or even leasing an apartment. Equifax, Experian, and TransUnion, the three national credit bureaus, collect this information and make it accessible on AnnualCreditReport.com, where it's legally free once per year. There are also multiple paid credit monitoring services to help you.
Your credit report is the first place to look if you suspect your identity's been stolen since it can show you any questionable or new activity. The FBI recommends checking your report at least once every 12 months, or more frequently if possible. Verify everything is accurate and up to date, and dispute and investigate actions or accounts that aren't.
Be mindful of public spaces
Public spaces are a great place to get some work done or use features and tools you don't have at your own facility — but practice caution with shared computers and networks in places like libraries, cafes, schools, and even grocery stores.
With public computers, you have no way of knowing the device's history or current security implementations. You don't know who the last person was that accessed it, what they used it for, or who the next person will be and what information they might be able to harvest after you've gone. Save any financial accounting, private transactions, or classified work for your personal device and log out of accounts and erase all browsing history and cookies before leaving.
Public Wi-Fi networks can also put your information at risk when you log onto unencrypted websites. These networks could let cybercriminals or nearby opportunists hijack your browsing session, access your personal files, or even get ahold of your login credentials to impersonate you and take hold of your accounts. Turn off autoconnect features on your phone or laptop so you can control which networks you connect to.
One way to protect yourself in public is by using a VPN service, which hides your IP address and encrypts the information you send online. Many VPN providers offer additional security features for even more protection at home and on the go.
Be mindful of physical threats in public, like people sitting behind you at the coffee shop who could look over your shoulder or see your login information through reflections. Never leave your devices unattended.
Shop on legitimate websites
Don't enter credit card information on a new web store unless you trust the website and have checked its security. You should also browse and shop with encryptions and safe browsing tools for added security.
Here are a few ways to determine whether the site you're browsing is safe to checkout with:
- Perform an online search with the name of the website and keywords like "scam," "fake," or "warning" to see if anything notable pops up
- Check out the URL — encrypted sites have read "HTTPS," not "HTTP"
- Check the web address for any typos, misspellings, or added or missing letters
- Investigate the website's other pages — does it have a contact form? An "about us" page?
- Read reviews of the website on third-party sites, like the Better Business Bureau and Trustpilot
- Note the webpage design — does it look professional, or does it have hard-to-read fonts and colors or excessive popups and ads?
- Read the site's security certificate by clicking the padlock icon in the address bar
Use safe online payment options and digital wallets for a more secure checkout and protection against fraud.
What to do if your identity is stolen
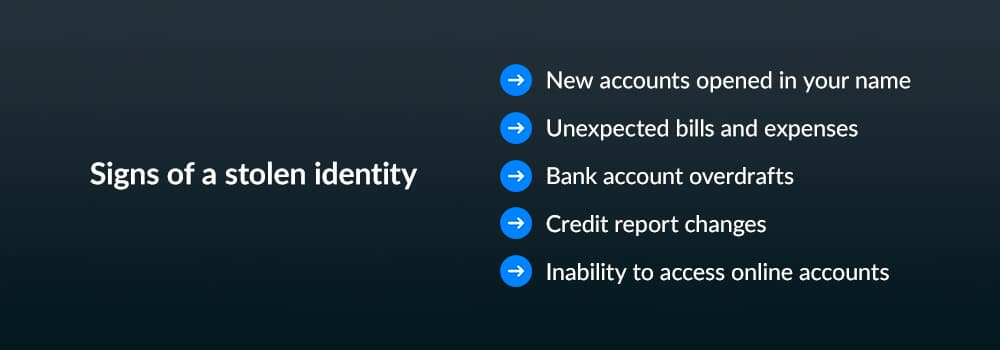
Signs of a stolen identity vary, depending on the nature of your business or online accounts, but keep a close eye on things like:
- New accounts opened in your name
- Unexpected bills and expenses
- Bank account overdrafts
- Credit report changes
- Inability to access online accounts
Follow these steps if you think your identity might have been compromised online:

1. Freeze accounts and reports
Once you think your identity has been stolen, freeze your credit report to protect it from further damage. Pause or lock the following:
- Digital wallets
- Credit cards
- Checking and savings accounts
- Streaming services
- Loyalty cards and membership programs
- Autopayment for utilities and bills
Keep a list of these accounts and any other financial or confidential information cybercriminals could access with your name and social security number or whatever information they've taken. Update and refer to this list as needed, so you can use it as a checklist if your identity is compromised in the future.
2. File a complaint
File an identity theft complaint with the Internet Crime Complaint Center (IC3), provided by IdentityTheft.gov. Have the following information ready:
- Your name and contact information
- Financial transaction information
- Any known information about the cybercriminal
- Details of the situation
- IP addresses
- Other relevant information that could help
Reporting the theft online will help the FTC and law enforcement track patterns or trends in your area and issue warnings as possible. They can also help you create and implement an identity recovery plan.

3. Consider insurance or recovery services
Monitoring and protection services are one way to prepare yourself for future identity theft concerns. By investing in these services now, you will be more prepared for damage control if your identity or online accounts are compromised. Consider the following:
- Identity theft protection: You can usually invest in identity theft protection and insurance through your financial institution, credit card provider, employee benefits program, or a third-party service. Recovery services can walk you through reinstating and saving your accounts and try to mitigate damage caused, but they can't guarantee any financial return if your money or wages were compromised.
- Homeowners insurance: Ask your homeowner or rental insurance provider about identity theft protection and online protection or insurance options to see what you can and cannot cover.
- Monitoring services: Identity and credit monitoring services can track your identity online. They'll inform you when they detect any significant changes, like changes on your credit report or a new social media account, loan application, or court case created in your name. Some services can even help you monitor your identity on places like the dark web, where scammers and cybercriminals share, buy, and sell information.
These services can be a great asset to your home or business, but always verify that you're working with a trusted, legitimate third party or a trusted partner. Never leave your insurance and recovery information where it could also be compromised.

How Box helps keep your data safe
All Box products and services support file encryption with AES 256-bit encryption across locations. Our system uses machine learning and top industry tools to defend your content and team from cyber threats, all while streamlining processes.
These are just some of the reliable security features you can expect with Intelligent Content Management from Box:
- Granular permissions
- User authentication
- Governance and compliance to avoid fines and meet global requirements
- Two-factor authentication for logins
- Multi-layered watermarking
- Native password controls
Box Shield also allows for classification-based policies and intelligent threat detection as you manage your entire content lifecycle with modifiable policies. You can choose when information is accessed, retained, saved, and how it's disposed of when finished.
Trusting Box for your productivity and workflow also gives you access to the Box Trust ecosystem. Enjoy easy integration with trusted third parties for security and compliance across your entire team, including:
- Different user and string tools
- Link expiration features
- Information rights management when externally sharing
- Native governance and discovery abilities
- Classification-based access control
- Native verification for device ownership
Stay up to date on everything happening inside and outside your team with in-depth audit logs and administrative reporting.
How Box KeySafe helps with online information protection
Box KeySafe is a unique security feature designed with your team's ultimate privacy and security in mind. It gives you independent control over all your encryption keys without interrupting the user experience in any way. Here's how it works:
- Upload a file to Box
- Box encrypts that file with a Box key
- You create your own encrypted key for an extra layer of protection
Box can never access your personalized encryption keys, and you can update your audit log or disable security team access as needed. KeySafe makes it easier to stay compliant and keep confidential information, like patient records or financial files, safe from third-party viewing and unauthorized access. Your log will show you all encrypted and decrypted data, and it's unchangeable, so you always know what's going on with your team and content.
Pair Box KeySafe and other services with your antivirus and other defensive tools for web browsing and content sharing, and you're setting yourself up for success.
Box brings you a secure and fully compliant platform so your teams can easily collaborate on content
Learn more about Box products and services
We live in a changing world full of innovative new technologies and online features that make it easier than ever to browse the web, get work done, and collaborate with distributed teams on work projects. With these conveniences comes an increased need for protection and awareness against growing threats of cybercrime. Knowing how to protect personal information online and relying on secure products for your work and home life are the best ways to keep yourself safe.
Box brings you a secure and fully compliant platform so your teams can easily collaborate on content. Get control over your content's complete lifecycle, all backed by encryption tools like KeySafe and access to our trusted ecosystem of partner integrations.
Learn more about Intelligent Content Management and compare pricing options to find the right fit for you.
**While we maintain our steadfast commitment to offering products and services with best-in-class privacy, security, and compliance, the information provided in this blogpost is not intended to constitute legal advice. We strongly encourage prospective and current customers to perform their own due diligence when assessing compliance with applicable laws.


